OAuth and API security in recruiting stacks
The set of authentication protocols, scoped token permissions, and integration security practices that govern how recruiting tools connect to each other and to candidate data - with OAuth being the dominant standard for granting limited access without sharing passwords.
Michal Juhas · Last reviewed May 4, 2026
What is OAuth and API security in recruiting stacks?
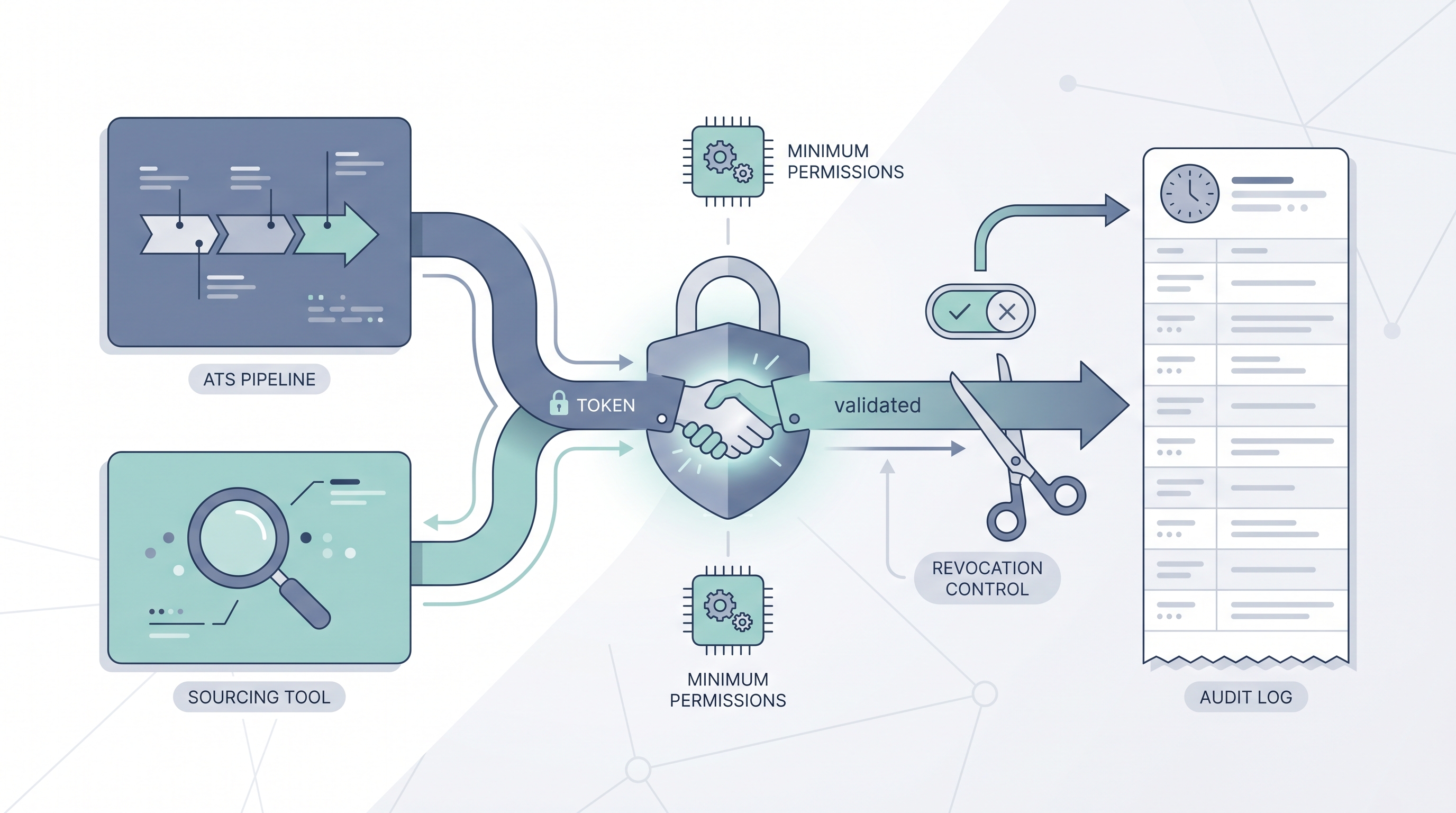
OAuth and API security in recruiting stacks refers to the authentication standards and integration hygiene practices that govern how your recruiting tools connect, share candidate data, and execute automated actions. OAuth is the most common authorization protocol used when one tool requests access to another: it issues a scoped token rather than sharing a password, making it possible to revoke access without disrupting the connected account.
API security extends beyond the handshake to cover how tokens are stored, what permissions they carry, how long they stay active, and whether anyone audits what they accessed. In recruiting stacks that connect an ATS, sourcing tools, enrichment vendors, and communication platforms, the API layer is where most data leaks and unauthorized-access incidents begin.
In practice
- When a TA ops manager says "we had a token leak," they mean an API key or OAuth token was exposed - often through a shared Postman collection or a Slack message - allowing someone outside the team to query or write to the ATS using the tool's permissions.
- A recruiter clicking "Connect to ATS" on a sourcing platform is authorizing an OAuth flow. The scopes they approve determine what that tool can do to candidate records, and most users accept all scopes without reviewing the list.
- A quarterly revocation audit, removing OAuth connections for vendors the team no longer uses, is the single most high-leverage security maintenance task for a small TA function without dedicated IT support.
Quick read, then how hiring teams use it
This is for recruiters, TA ops, and HR leaders who need to understand integration security well enough to make smart vendor decisions, run basic audits, and answer compliance questions. Skim the first section for the vocabulary. Use the second when you are configuring live integrations.
Plain-language summary
- What it means for you: Every time you click "Authorize" to connect a recruiting tool to your ATS or email, you are issuing a credential that carries real permissions. Treat it like a key to the office.
- How you would use it: Review the permission scopes before authorizing any new integration. Document active tokens somewhere the team can see and update them. Set a reminder to revoke unused connections every quarter.
- How to get started: Open your ATS admin panel and list every active OAuth connection. For each one, confirm the vendor is still in use, the scopes are still appropriate, and the DPA is signed.
- When it is a good time: Before any new vendor goes live and during any vendor offboarding.
When you are running live reqs and tools
- What it means for you: Over-permissioned tokens and unrevoked connections from past vendors are the leading causes of unauthorized data access in recruiting stacks. They are also the hardest to detect because no alert fires when a stale token is used.
- When it is a good time: Audit tokens whenever a vendor relationship ends, when a team member with admin access leaves, and quarterly as a standard hygiene check.
- How to use it: Scope every token to minimum necessary permissions. Store credentials in a team vault, not in shared documents or chat. Log API calls at the ATS level and review anomalies monthly.
- How to get started: Map each integration in your stack against three questions: what data can it read, what can it write, and when was the token last reviewed? Fix any that answer "full access" or "never."
- What to watch for: Integrations that bundle too many scopes into a single authorization request, vendors who cannot provide a clear DPA, and webhooks configured to retry on failure without a dead-letter inbox.
Where we talk about this
On AI with Michal live sessions integration security comes up in the sourcing automation track every time we wire a new tool to an ATS: we stop at each token request and walk through scope review, credential storage, and what to log. The AI in recruiting track covers the policy side: how to explain API security to a GDPR officer, what to include in a vendor data flow map, and how to write a one-page integration security standard a small TA team can actually follow. Bring your current tool list to Workshops.
Around the web (opinions and rabbit holes)
Third-party content on API security ranges from deeply technical to practitioner-friendly. These links are starting points; verify any advice against your ATS vendor documentation and your legal team.
YouTube
- OAuth 2.0 explained simply covers the token flow in plain language without requiring a developer background.
- API security best practices includes token scoping, rotation, and audit logging walkthroughs relevant to SaaS stack management.
- GDPR and recruiting software integrations covers compliance angles that apply when you connect sourcing tools to ATS platforms across EU jurisdictions.
- ATS API security questions in r/recruiting surfaces practical questions from TA ops teams managing vendor integrations without dedicated IT support.
- OAuth token management for SaaS stacks in r/sysadmin gives IT-side perspective on the same problems TA ops teams encounter.
- Webhook security recruiting in r/recruiting covers error handling and data leakage stories from practitioners who built integrations and found problems later.
Quora
- How do I secure recruiting tool integrations? gathers advice from practitioners and IT professionals; read alongside your ATS vendor documentation.
OAuth versus API key: when to use which
| Credential type | Best for | Key risk |
|---|---|---|
| OAuth token (scoped) | User-authorized third-party tools | Over-permissioned scopes at authorization |
| API key (service account) | Server-to-server automation | Leaked key has full scope until rotated |
| OAuth with refresh tokens | Long-running integrations | Refresh token stored insecurely |
Related on this site
- Glossary: ATS API integration, Recruiting webhooks, Workflow automation, Applicant tracking software, Candidate data enrichment
- Guides: Sourcers
- Workshops: AI in recruiting
- Membership: Become a member
- Courses: Starting with AI: the foundations in recruiting
